Federal IT structure: How minimum security requirements can be achieved

Fulfillment of the requirements from the IT-Grundschutz (IT-GS) is mandatory, among other things, for all federal IT protection objects as part of the security procedure. This ensures that the Confederation's IT infrastructure consistently meets the minimum security requirements or how these can be achieved. Version 5.0 of the IT-Grundschutz is valid from March 1, 2022, and thus replaces the previous version IKT-GS 4.6. In principle, the new version pursues the same goal, but has been adapted in places. These adjustments are explained in the blog in a practical manner in order to enable application managers in operations as well as ISDS managers (responsible for information security and data protection aspects in a project) and project managers in the context of HERMES projects a smooth introduction to IT-Grundschutz 5.0.
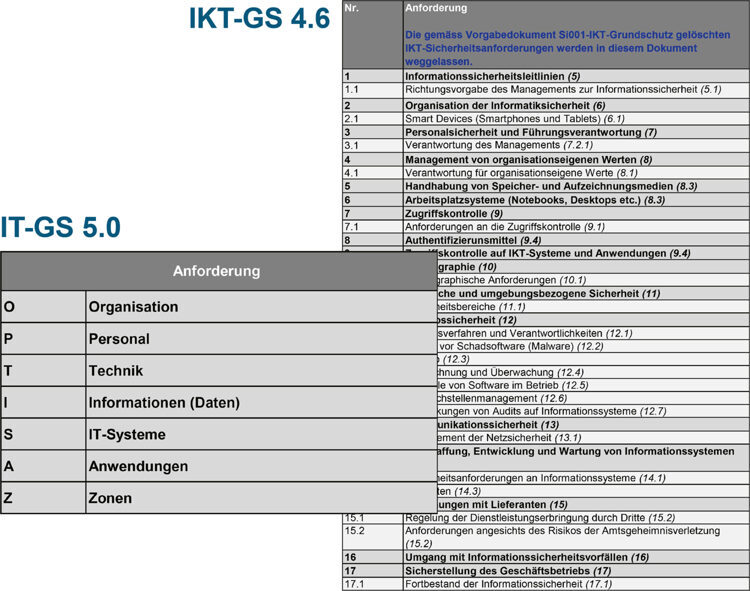
The former IT-Grundschutz was based on ISO 27002:2013 in terms of content and structure. The new IT-Grundschutz, on the other hand, is based on the new ISO 27002:2022, which entails fundamental structural changes to the standard: Instead of 14 chapters, there are now only five topic blocks on Organizational Controls, People Controls, Physical Controls and Technological Controls. The structural changes in ISO 27002 are reflected analogously by the restructuring of IT-GS 5.0 and thus emphasize the orientation to the ISO 27000 series.
In ICT-GS 4.6, the bracketed, italicized numbers, such as (6.2.1), used to refer directly to the corresponding control in Annex A of ISO 27001 or ISO 27002 for each requirement. However, such direct references are deliberately no longer listed in the new IT-Grundschutz. The certification of a provider or a service provider in accordance with ISO 27001, which remains unchanged in contrast to ISO 27002, is still a robust indicator of the implementation of IT-GS 5.0. However, this does not exempt the service provider from a conscientious audit, as is required in the wording for the signatures.
In the ICT SG 4.6, the responsibility for implementation was explicitly assigned to the benefit recipients (BP), benefit providers (FP) and/or users (UP) for the different requirements. This is no longer the case in the new version.
"By their signatures, the undersigned confirm that the requirements of Si001 version 5.0 are implemented and met and that, in their opinion, all service providers (SPs) involved in the operation of the protected object also meet the requirements that apply to them."
The responsibility for the protected object and the critical examination of the implementation of the requirements is now clearly assigned to the benefit recipient. For protected objects with several service providers (developers*, operation, hosting/computing center, service/support, etc.), this is a welcome development, but it poses the challenge for the LBs to decide independently in which cases the definition of a protected object is in line with the objective.
"The requirements that [...] are marked with an asterisk (*) are less risky from the perspective of IT security for the federal administration. Deviations are possible for them if they are justified and documented in the document Implementing measures for ICT basic protection or in the ISDS concept."
The practical interpretation of this: IT-Grundschutz 5.0 must cover a very broad, heterogeneous field of protection objects. Complete fulfillment of all requirements, as was previously communicated in parts (subject to the classification of requirements as "Not relevant"), is neither possible nor expedient for many objects of protection. The adaptations here bring the necessary flexibility to specifically process the rather general requirements on the objects of protection.
If not all requirements of IT-Grundschutz 5.0 can be met, these deviations must be treated as exceptions. The explanations are summarized below and augmented by the author:
If [...] cannot meet one or more of the requirements of the IT-GS, it needs an exemption according to [...] Cyber Risk Ordinance (CyRV). This can be obtained in one of the following three ways, ranked as increasing "escalation levels":
- IT-GS: Justified shortfalls of the requirements marked with an asterisk (*) are automatically granted as an exception upon release of the IT-GS.
- ISBD: An Information Security Officer Department (ISBD) may approve a formal exception request or delegate [...] to the ISBO [...] if all of the following are met:
a) The ISBD is involved in the exception approval process in a manner that allows it to carry out its responsibilities
b)In summary, the exception applies exclusively to objects of protection or information of the VE without an increased need for protection. Comment on this: Increased need for protection exists as soon as one of the classification fields in the protection needs analysis is marked as red in the area of confidentiality and/or if more than two criteria in the areas of availability, integrity or traceability are marked as red. - P035: All other exception requests can be submitted through the Federal ICT Requirements and Specifications Management process (process P035, see references) for the attention of the National Cyber Security Center (NCSC). However, this point will not be discussed further in this paper.
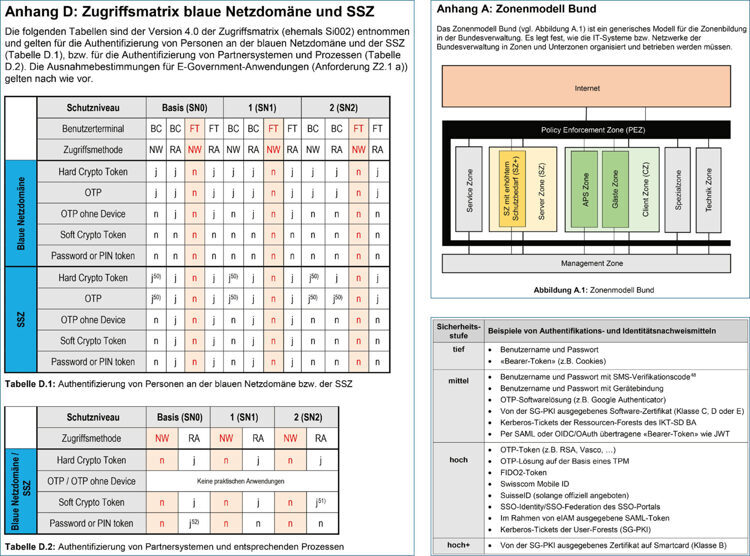
Compared with ICT-GS 4.6, IT-GS 5.0 deals increasingly explicitly with the appropriate security of the network environment and the protected objects operated in it. Policies or guidelines are defined via the (network) zones, which control the scope of the security requirements for access and authentication.
As a result, formerly stand-alone documents have now been incorporated directly into the appendix as:
- Appendix A: Federal Zone Model
- Appendix B: Security Levels for Authentication and Identity Proofing Means
- Appendix C: Zone policy "network domain blue"
- Appendix D: Access matrix blue network domain and shared service zone (SSZ).
It is worthwhile to study the appendices in detail, especially with regard to requirements Z2.1 (access to the zone for persons and automated processes) and O2.2 (operation of the protected object outside the federal administration zone).
"For applications, the person responsible for the application in accordance with the role description of the federal government's IT processes (see reference to P000)."
For applications, the role owners of the protection object are generally on the benefit recipient (BP) side and are more operationally involved with the protection object. The inclusion of role owners who are more familiar with the protection object from an operational perspective is a welcome development, especially for the validation of documents that are initially created in projects, but then need to be managed in operations. In addition to (1) the ISBO, (2) the principal*, (3) the business process owner*, and (4) the PI owner or member of management, IT-GS 5.0 also adds (5) the protection object owner.
Conclusion
The new version of IT-Grundschutz consistently brings improvements without breaking with the fundamental principles and objectives. An update of the IT-Grundschutz must take place at the latest within the regular life cycle of the security documentation, which is a maximum of five years since approval. When migrating from ICT-GS 4.6 (or older) to IT-GS 5.0, a fundamental, "free" editing of the new IT-Grundschutz leads to faster and better results than if assessments are copied directly from ICT-GS 4.6 to IT-GS 5.0.
Extraordinary situations require a new mindset. This article discusses why the path to a zero-CO2 society is considered inevitable and why this aspect should be integrated into our daily thoughts and actions as soon as possible.
In recent years, numerous energy utilities have begun to optimize their business processes, diversify their revenue base and seek out new service areas. The transformation is in full swing.
We have compiled reports on our projects, interesting facts from the various competence and customer areas as well as information about our company for you here.
Our vacancies
NCSC Homepage > Documentation > Federal IT Security Requirements > Security Procedures > Basic Protection.
Si001 - IT baseline protection in the federal administration - version 5.0 (PDF)
Si001 - Hi01: Implementation of measures for IT-Grundschutz in the Federal Administration - Version 5.0 (XLS)
BK Homepage > Digital Transformation and ICT Governance > Requirements > Processes and methods > P000 - IT processes in the federal administration
P041 - Protection requirements analysis - Version 4.5 (PDF, 344 kB, 19.04.2021)
BK Homepage > Digital Transformation and ICT Governance > Requirements > Processes and methods > P035 - Dealing with requirements and requirements for federal IT
